Community Of Purpose driving to new levels with support from BOM IT
Andy Carter Managing Director of BOM is delighted to announce the continued support of Community of Purpose CIC. "As a People First Company, BOM IT Solutions are incredibly proud to be able to support this great not-for-profit and make a difference to the young...
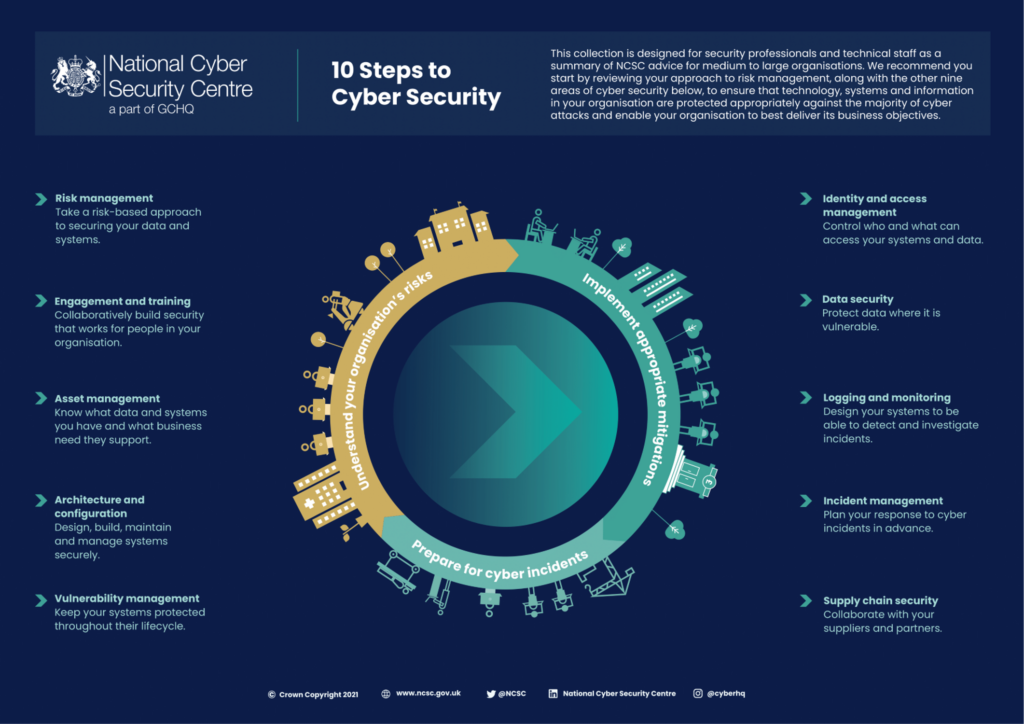
Why cyber must be a priority for small businesses
Why cyber must be a priority for small businesses
How to enhance your email security
When the first email was sent in 1971, few would have imagined just how important a role this new method of communication would go on to play in business and commerce today...
The Five Benefits of Outsourced IT
For businesses today, IT is vast, with many different systems running parallel to one another. Whether it’s cybersecurity, e-commerce, digital device management, or data services – most companies are using an array of different products and services to make up...
BOM IT Solutions has been shortlisted for the mid-enterprise MSP of the Year
We are delighted to announce that BOM IT Solutions has been shortlisted for the mid-enterprise MSP of the Year category at the Technology Reseller Awards! ???? The Technology Reseller Awards recognise and celebrate businesses throughout the IT channel, highlighting...
Top five reasons why companies are refused cyber insurance
Only 43% of businesses today hold an insurance policy that covers cyber risks. That’s according to the latest Government Cyber Security Breaches Survey. Yet, if you read any cybercrime statistics, cyberattacks are only going one way – and that’s up. Cybersecurity...
UK Cyber Resilience Legislation: What is it and what does it mean for you?
The UK has seen a drastic leap in cyber-attacks in recent years. In 2022, 39% of UK businesses reported being the target of a cyber breach in the previous 12 months, which highlights just how many businesses are struggling to remain secure online. Smaller...
How can businesses reduce their electronic waste?
With the pressure continuing to mount on UK businesses to decarbonise in line with the government’s 2050 net zero guidelines, companies are looking at innovative ways to reduce the impact that their business operations and services have on the climate, environment,...
BOM have a unique offering that allows you to extend your device life with support for 5 years or more!
What happens when the warranty of your device expires, and the hardware becomes redundant? How do you manage your environmental responsibility and sustainability issues associated with this? For more information please see BOM's specific "Device Life Support"...
Supporting Southwest Charities “People First”
Our People First Technology's Covered philosophy makes us proud to support these organisations & charities in a variety of ways: If you'd like any introductions to our charity community contacts please don't hesitate to contact us For more information here are...